Our Network Vulnerability Assessment and Penetration Testing service is designed to help organizations identify and mitigate potential security risks within their network infrastructure. Our team of certified security professionals will use a combination of automated tools and manual testing methods to thoroughly scan your network for vulnerabilities and simulate real-world attacks to identify any weaknesses that could be exploited by cybercriminals.
Benefits of Service
- Identify and prioritize vulnerabilities within your network infrastructure
- Understand the potential impact of identified vulnerabilities on your organization
- Validate the effectiveness of existing security controls
- Provide recommendations for remediation and mitigation of identified vulnerabilities
- Improve overall network security and reduce the risk of data breaches
Approach & Methodology
Our approach to Network Vulnerability Assessment and Penetration Testing is based on a framework that includes the following stages:

-
Planning and Preparation : This stage involves identifying the scope of the assessment, determining the objectives and goals, and establishing the testing environment.
-
Information Gathering : In this stage, we gather information about the network infrastructure, including IP addresses, network topology, and services running on the network
-

Vulnerability Scanning : Automated tools are used to scan the network for vulnerabilities and identify potential points of attack.
-

Penetration Testing : Our team of security professionals will simulate real-world attacks to identify any weaknesses that could be exploited by cybercriminals.
-

Reporting : We will provide a detailed report of our findings, including recommendations for remediation and mitigation of identified vulnerabilities.
-

Follow-up : We will follow up with your organization to ensure that the recommended remediation and mitigation measures have been implemented and that the network is secure.

Frequently Asked Questions
The number, variety, and complexity of threats are growing at an alarming rate. Many specialists in the field of cybersecurity have seen a dramatic increase in external cyber assaults, particularly those launched by criminal groups and foreign governments.
The ease of mobile devices and the ability to be "online all the time" are two major benefits. Mobile devices have been extensively used by governments for the purposes of increasing access to government resources and the efficiency of government employees.
However, there are inherent security concerns and additional points of entry to the network when mobile devices are used for communication and data exchange. It's undeniable that mobile malware risks are on the rise, and lost or stolen devices are a major mobile security risk.
The usage of one's own mobile device at work, as well as the need for user identification, both pose additional dangers. A variety of recommendations for government agencies may be found in the NIST paper "Guidelines for Managing the Security of Mobile Devices in the Enterprise" (SP 800-124).
Cybersecurity spending should go toward developing capacities like cyber tools and education. However, cyber security cannot be an afterthought in the planning stages of any project, programme, or management effort; rather, it must be "baked into" each one from the start. Every company should include cyber security funding in their annual budget since it is a necessary expense.
People know something about cyber security, but not enough to keep themselves safe. Most people probably also know how important it is to keep data safe and that cyber threats are getting worse.Effective cyber security, on the other hand, is something that both the government as a whole and the people who work for or are served by the state government need to keep working on.
This ability needs to be used, tested, and improved on a regular basis through awareness training in order to fight not only aggressive cyber threats, but also cyber events that happen by accident.
Yes. Cloud services promise to offer flexibility, scalability, measured service, and some cost savings, but they also pose more security risks when it comes to accessing and storing government data and authenticating users.
When judging cloud computing in general and the different deployment models, it's important to know how much cloud services cost and how safe they are (public, private, hybrid, community). Cloud services made for consumers that are used by government workers pose extra risks because they might not have strict security controls.
- Describe their current state of cyber security and where they want to be in terms of cyber security.
- Identify and rank opportunities for improvement in a process that is ongoing and can be repeated;
- Check how close you are to your goal;
- Talk about cyber security risk with both internal and external stakeholders.
Our Trusted Clients Feedback
With Be4Breach, we're fanatical about one thing: They are creating amazing products & services that combine security, simplicity, and affordability. Organizations of all types and sizes - from small businesses to very large enterprises - are relying on Be4Breach for information security.

Car Expert/ Top IT Team

If you’re looking for the opportunity to work with a company that really understands the penetration testing space and is really forward-looking in how they do it, BE4BREACH’s an excellent option… it really is the complete package to help build out a program and augment what you’re doing internally

Explico

We would like to thank you for your support in Gap analysis and completion of audit smoothly. During the complete audit we found Be4Breach team to be very supportive and cooperative which lead the audit completion in time . Once again thanks for getting successful Audit.

Netsach

We secured lifecycle management in Blockchain implementations with the support of Be4Breach's team of Blockchain security experts, architects, and engineers. Their team is qualified to provide the necessary security audits, penetration testing, and remediation services, as well as experience

BharatVerse

You have been very helpful and professional in designing the entire audit, thoroughly finding the gaps, helping us in closure of each and every gap and then conducting the post gap assessment audit. It was an extremely well done exercise. Every feedback that you gave for our various processes .

TechDriver

Overall, we were very satisfied with Be4Breach's services. They were quick to respond to questions and concerns, clear in their explanations, and thorough in their testing and reporting. We have more trust in the security of our app now, and we will continue to engage their service as we expand.

Clevoir



Latest Blog Post
- Jul 08, 2021
- 1 Comment
Here Are Five Measures Tech Firms Can Take to Halt Data Breaches
Thanks to the efforts of the IT sector, digital transformation has been able to permeate all industries. The majority of...
- Jul 08, 2021
- No Comments
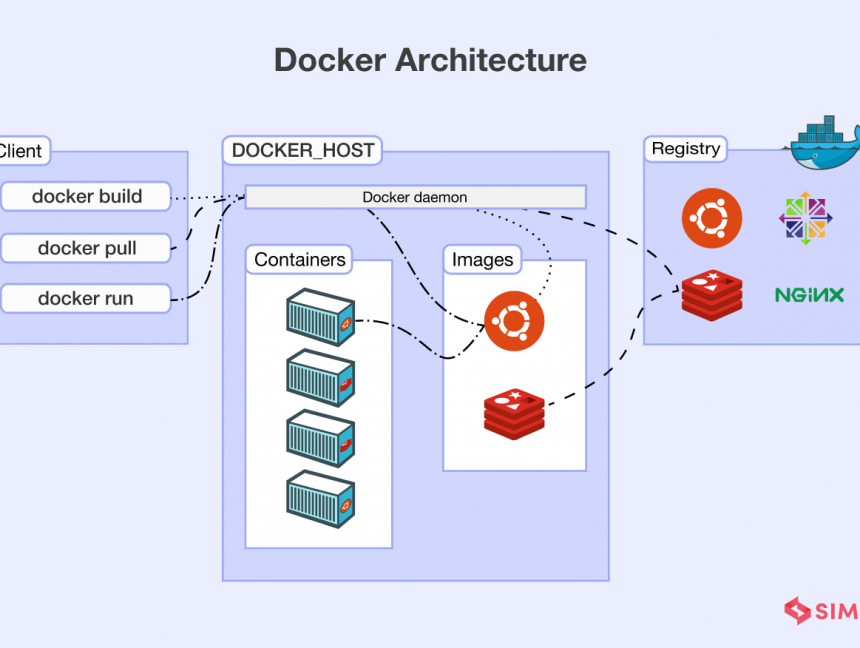
Docker’s Five Most Unusual and Amazing Use Cases
Develop a platform like GitHub. Do you wish there was a way to keep your repositories away from the internet?...
- Jul 08, 2021
- No Comments
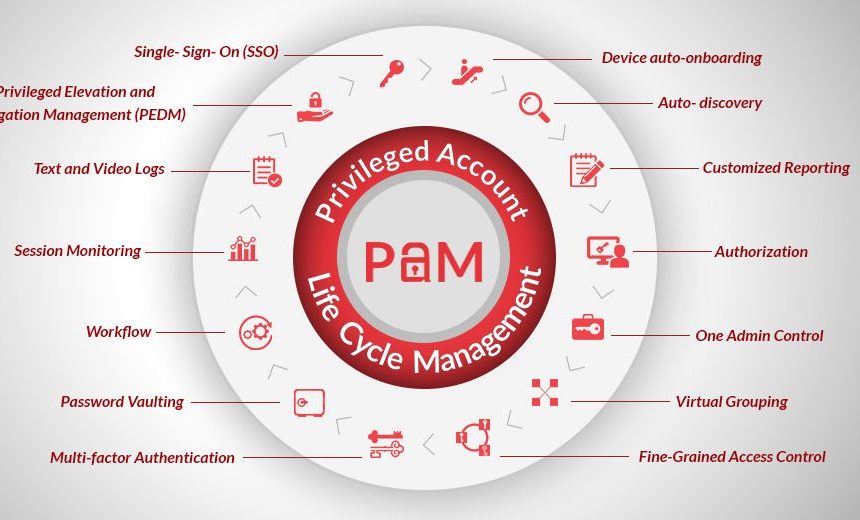
Critical PAM controls for modern cloud environments
Failures and breaches in cloud security are often brought on by improper administration of user identities, permissions, and other related...